Compliance Management
Iotellect Network Manager can test device configurations for compliance with federal regulations (such as PCI, HIPAA or SOX) or corporate security standards. All violations are immediately detected and system operators get warned.
The compliance policies are rule-based. The Network Manager distribution includes a number of standard policies. However, existing policies can be fine-tuned and new policies can be added on-demand.
Changed and newly created policies can be easily tested against any configuration. However, normal system operation assumes that compliance is automatically checked each time a configuration change is detected. This makes spot violation statistics available at any time, in addition to scheduled reporting.
Typical configuration problems can be automatically remediated by launching a configuration script upon a Policy Violation alert.
Compliance Policies
A compliance policy is a set of rules to check device configuration against. If a configuration matches all rules in a policy, it's called a compliant configuration. If one or more rules are not satisfied, the configuration is said to violate the policy.
Administering Compliance Policies
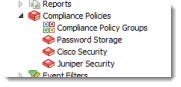
This section explains how to manage compliance policies. Iotellect Network Manager represents each policy as a separate context that can be managed like any other contexts (e.g. alerts or reports).
Two contexts are used to administer compliance policies: One is the general Compliance Policies context which serves as a container. The other is the Compliance Policy context which holds rules of a single policy. |
|
Applying Policies
After initial configuration of Compliance Policies it's necessary to associate selected policies with certain devices to force the server to check each new configuration backup for possible violations.
Device-specific compliance management is controlled via Compliance Policies table that can be accessed via Edit Device Properties dialog. The table allows to select multiple Compliance Policy contexts to check device configurations against.
Compliance Checking
After some compliance policies are applied to a device, compliance of its configuration to those policies is checked each time a new configuration backup is made.
To force checking historical device configurations to currently applied policies, run Check Compliance action of any device which configurations were backed up at least once.
Policy Violation Reporting
Each device that has assigned compliance policies reports current policy violations in its status. To see a violation list:
- Right-click on a device
- Run View Status actions
- Switch to Compliance Policies Violations tab
The violation list record describes:
- Date/time of policy violations check
- Date/time of configuration backup
- Configuration type
- Configuration label
- Violated policy description
- Violated policy rule description
- Rule severity level
- Violated rule's expression
- Line number (for rules working in Line mode)
Policy violation list is persistently preserved in the database and, thus, available even immediately after the server startup.
Policy Violation Alerting
Each time a new policy violation is detected, Iotellect Network Manager fires a Policy Violation event in Administration context. It's easy to setup an alert that will react to new violation events and, for example, send e-mail or SMS notifications to security specialists.
Was this page helpful?